Who is MODSIM for within the enterprise ecosystem?
In the context of increasing competitive pressure and the demand for continuous innovation...
MODSIM — A New Approach to Design and Simulation Collaboration
The concept of MODSIM is formed by combining two terms: Modeling and Simulation. To begin,...
TOP New Features in CATIA V6 2024
CATIA 2024 is a major upgrade that delivers numerous new features and enhancements designe...
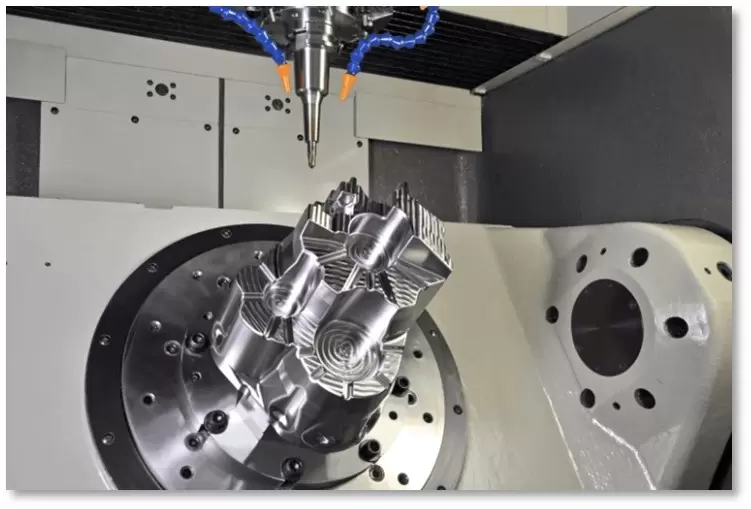
COMPARISON OF CAM-TOOL PRIME / 3+2 AXIS / 5 AXIS MODULES
CAM-TOOL software is a widely used CAM system in the mold and die industry. Let’s explore...
Information Security for the Accounting Department
Data in general, and accounting data in particular, is confidential information for every...
Overview of the 3D CAD/CAM/CAE Solution System for Design, Simulation, and Manufacturing – CADmeister – Part 2
In Part 1, we provided an overall introduction to the CADmeister software. In Part 2, let’...
Introduction to Trend Micro Email Security
Email impersonation is a preferred attack method used by hackers, alongside ransomware and...
New System Vietnam’s ITMA 2023 Workshop with Customers
In July, New System Vietnam successfully organized a series of ITMA workshops on cybersecu...
OVERVIEW OF 3D CAD/CAM/CAE SOLUTION SYSTEM FOR DESIGN, SIMULATION, AND MANUFACTURING – CADmeister
CADmeister is a comprehensive CAD/CAM/CAE software solution widely used across various ind...
Improvements to the Z-Level Rough Cutting with Multi-Tool Command in CAM-TOOL V18.1
Enhancements in CAM-TOOL Design Software Version V18.1
CYAS AND E-LEARNING SOLUTIONS FOR ENTERPRISES
Email-based cyberattacks remain a constant threat to businesses of all sizes. So what solu...
3D Integrated CAD/CAM System – CADmeister 2022
CADmeister was first launched by UEL in July 2005 and is the only 3D integrated CAD/CAM sy...