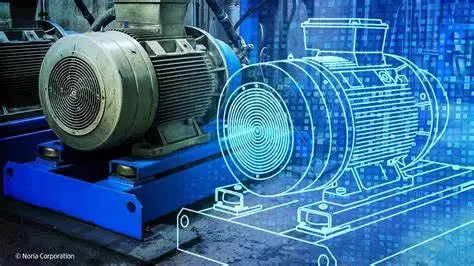
Applications of Digital Twins in Industrial Sectors
The Digital Twin lies at the heart of the shift from simple electronic control to a boundl...
Discover the Generative Design approach with 3DEXPERIENCE CATIA.
How can we continuously optimize materials and improve products? What methods can simplify...
Apex One: The Endpoint Security Expert for Businesses
Why is Trend Micro Apex One considered the pinnacle of endpoint security? What benefits do...
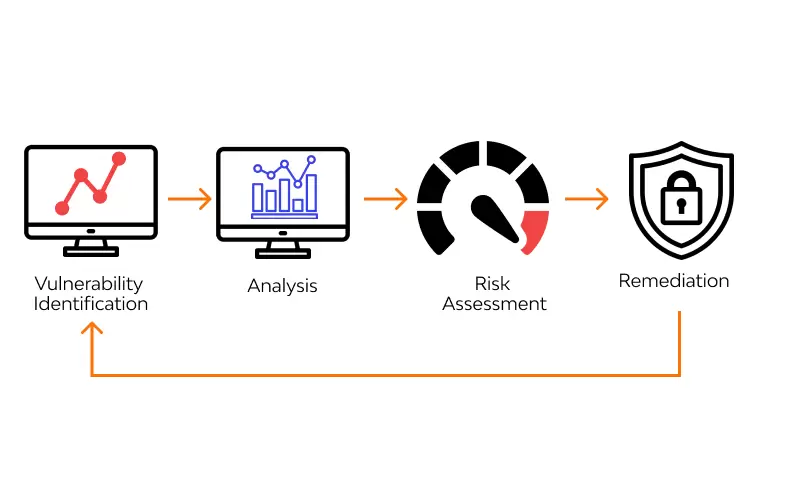
Internal Security Assessment and Penetration Testing Solution – Internal Platform Diagnostic
Following our previous article on external system security assessment and penetration test...
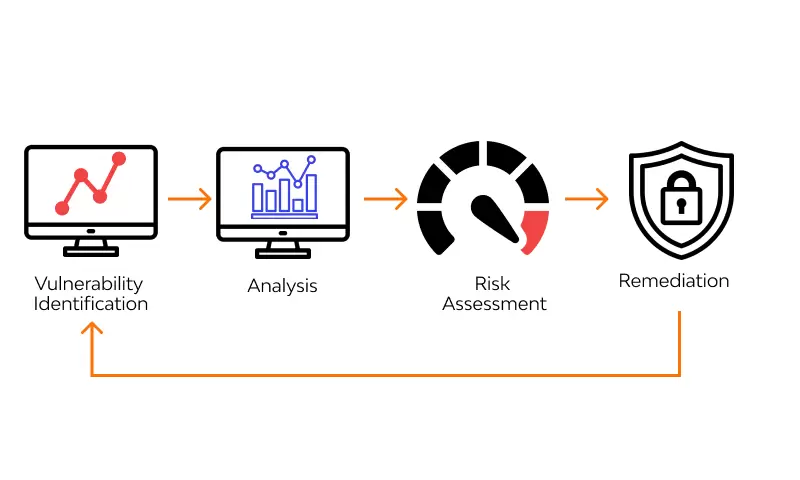
External Security Testing Assessment Solution – External Platform Diagnostic
In the era of Industry 4.0, cities are becoming increasingly dynamic, and the rhythm of da...
The Importance of Endpoint Detection and Response (EDR) – Endpoint Protection & Response
Today, as cyberattacks become increasingly sophisticated, establishing advanced threat pro...
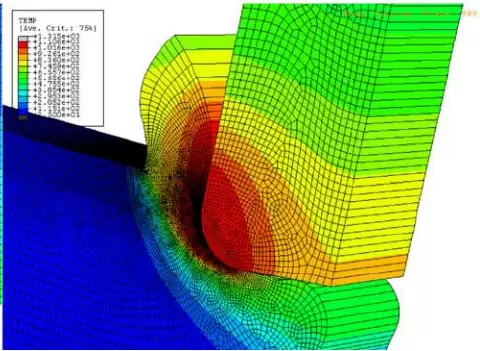
Mechanical Machining Simulation Using SIMULIA Abaqus FEA
Machining is one of the most important manufacturing processes, widely used in modern indu...
What Makes Cylance Protect a World-Class Cybersecurity Solution
Cylance Protect is an AI-powered cybersecurity solution designed to prevent cyberattacks....
Africa: Rising Cyberattacks, Especially Online Fraud
A recent report revealed that although ransomware attacks are “rapidly expanding” across A...
7 Steps to Prevent and Minimize the Impact of Ransomware
7 Steps to Prevent and Minimize the Impact of Ransomware
From small organizations to larg...
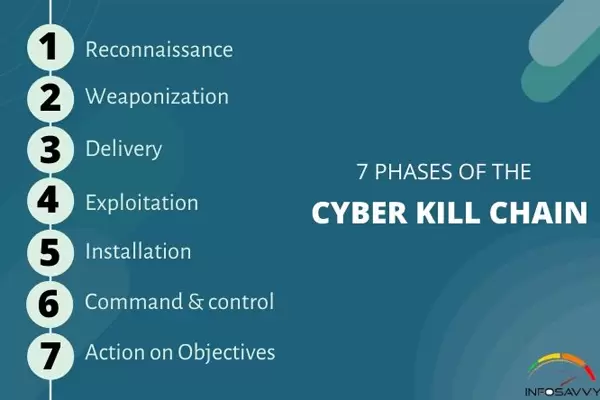
The Seven Stages of a Cyberattack
If identified early, the seven stages of a cyberattack provide a foundation for understand...
What is social engineering? How can we prevent it?
Social engineering, also known as non-technical attacks, is the art of manipulating users...