The Importance of Endpoint Detection and Response (EDR) – Endpoint Protection & Response
Today, as cyberattacks become increasingly sophisticated, establishing advanced threat pro...
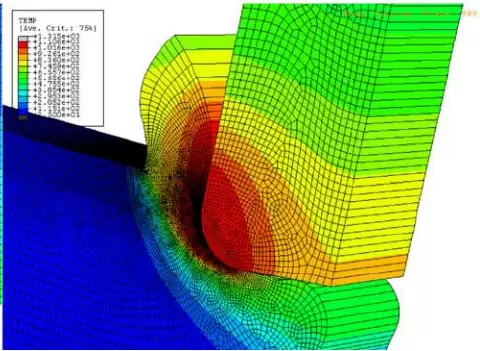
Mechanical Machining Simulation Using SIMULIA Abaqus FEA
Machining is one of the most important manufacturing processes, widely used in modern indu...
What Makes Cylance Protect a World-Class Cybersecurity Solution
Cylance Protect is an AI-powered cybersecurity solution designed to prevent cyberattacks....
Africa: Rising Cyberattacks, Especially Online Fraud
A recent report revealed that although ransomware attacks are “rapidly expanding” across A...
7 Steps to Prevent and Minimize the Impact of Ransomware
7 Steps to Prevent and Minimize the Impact of Ransomware
From small organizations to larg...
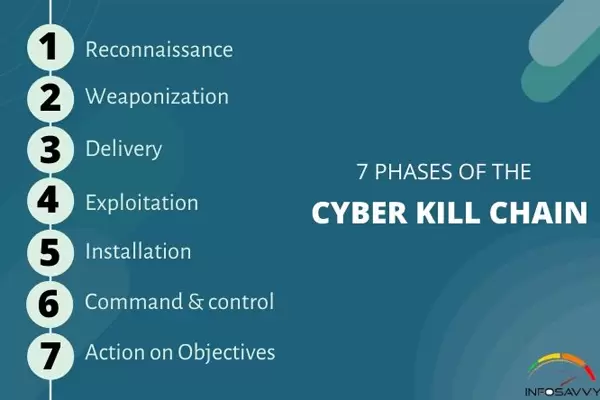
The Seven Stages of a Cyberattack
If identified early, the seven stages of a cyberattack provide a foundation for understand...
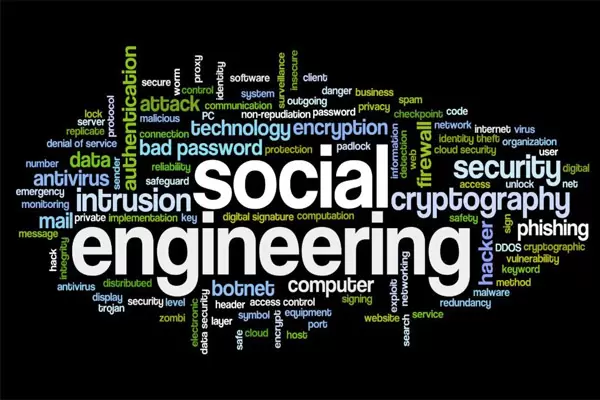
What is social engineering? How can we prevent it?
Social engineering, also known as non-technical attacks, is the art of manipulating users...
What is a DDoS attack?
A DDoS attack is one of the most terrifying threats in the IT world. Distributed Denial of...
Top 14 Best Vulnerability Scanning Tools Today
The top 14 vulnerability scanning tools recommended by experts help organizations and busi...
What is cybercrime? How can you protect yourself against cybercrime?
Cybercrime, also known as computer crime, refers to individuals who use computers as tools...
Top Hottest Cyberattacks in the World in 2020 (Part 2)
Top Hottest Cyberattacks in the World in 2020 (Part 2) – In this article, NSV continues to...
Top Hottest Cyberattacks in the World in 2020
The hottest cyberattacks in the world in 2020 (Part 1) are events we need to look back on...